Today, we are going to discuss about the various phases of Hacking which a Hacker must follow to implement a successful attack.
We have a lot to discuss, so let’s get started!
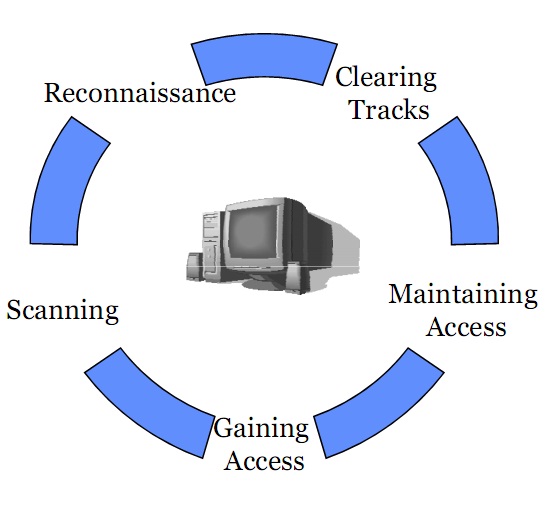
Five Phases of Hacking:-
The five phases of Hacking are as follow:
- Reconnaissance
- Scanning
- Gaining Access
- Maintaining Access
- Covering Tracks
Reconnaissance:- This is the primary phase where the Hacker tries to collect as much information as possible about the target. It includes Identifying the Target, finding out the target’s IP Address Range, Network, DNS records, etc.
Scanning:- It involves taking the information discovered during reconnaissance and using it to examine the network. Tools that a hacker may employ during the scanning phase can include dialers, port scanners, network mappers, sweepers, and vulnerability scanners. Hackers are seeking any information that can help them perpetrate attack such as computer names, IP addresses, and user accounts.
Gaining Access:- After scanning, the hacker designs the blueprint of the network of the target with the help of data collected during Phase 1 and Phase 2. This is the phase where the real hacking takes place. Vulnerabilities discovered during the reconnaissance and scanning phase are now exploited to gain access. The method of connection the hacker uses for an exploit can be a local area network (LAN, either wired or wireless), local access to a PC, the Internet, or offline. Examples include stack based buffer overflows, denial of service (DoS), and session hijacking. These topics will be discussed in later chapters. Gaining access is known in the hacker world as owning the system.
Maintaining Access:- Once a hacker has gained access, they want to keep that access for future exploitation and attacks. Sometimes, hackers harden the system from other hackers or security personnel by securing their exclusive access with backdoors, rootkits, and Trojans. Once the hacker owns the system, they can use it as a base to launch additional attacks. In this case, the owned system is sometimes referred to as a zombie system.
Covering Tracks:- Once hackers have been able to gain and maintain access, they cover their tracks to avoid detection by security personnel, to continue to use the owned system, to remove evidence of hacking, or to avoid legal action. Hackers try to remove all traces of the attack, such as log files or intrusion detection system (IDS) alarms. Examples of activities during this phase of the attack include steganography, the use of tunneling protocols, and altering log files.
That’s it for now. Be sure to check other cool stuff at Hacoder.
Any questions, comments or suggestions are welcomed.